whoami
A brief introduction to who I am and what I do

Senior Security Researcher
Cybersecurity Enthusiast and Certified Ethical Hacker from India with 5+ years of hands-on experience in Application Security, Penetration Testing, Bug Bounty Hunting, and Security Research. Currently working as a Senior Application Security Engineer at Loginsoft, specializing in Penetration Testing across web, mobile, API, networks, and cloud environments, DAST, SAST, SCA, and Source Code Review.
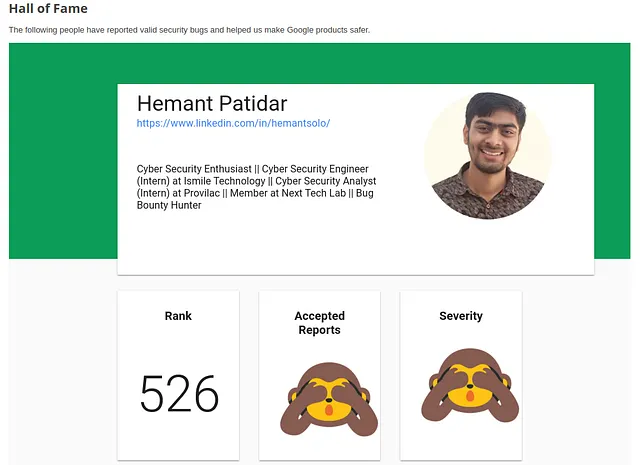
Holder of industry-leading certifications including CEH Master, eWPTXv2, eCPPTv2, eJPT, CAPen, CAP, and CNSP. Author of 10+ CVE vulnerabilities and finder of 5,000+ valid security bugs. Recognized with Hall of Fames and bounty awards from Apple, Google, Meta, U.S. Department of Defense, Cisco, Netflix, Mastercard, Ferrari, and 100+ organizations worldwide. All-Time Top 10 on Yogosha with €50,000+ in bounties earned.